Here’s Why Kaspersky Says PowerGhost Is The Malware Of The Future

PowerShell is Microsoft’s new method for enabling system and network administrators to work with command lines, providing them with a more advanced scripting system where they can automate routine tasks. If you recall, it played the role of the MS-DOS-era Command Prompt many decades ago. But because anything that can be done in the GUI can also be done through PowerShell—more than what Command Prompt offers—it is an attack surface most system admins have not blocked. If it were blocked, the PowerShell scripts would not successfully run.
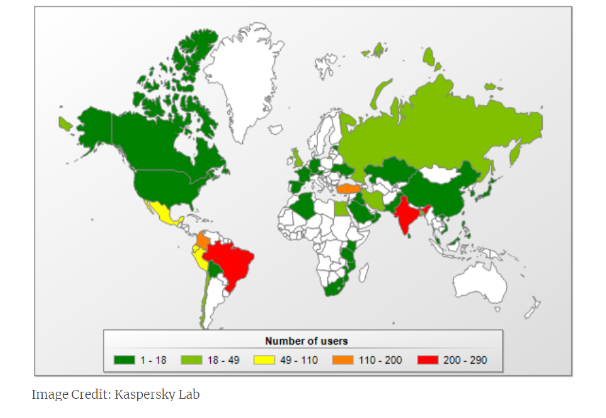
The theory was proven correct when the Russian antivirus firm, Kaspersky Labs, discovered PowerGhost, a custom PowerShell script which operates as malware. Currently infecting many corporate network installations, PowerShell is designed to run and deploy scripts easily while enabling routine IT tasks by default. As a cryptocurrency mining tool, PowerGhost is essentially disguised within PowerShell packaging. It cleverly takes advantage of all Windows APIs and functionality of the PowerShell scripting system to completely infect a machine in the name of cryptocurrency mining.
Kaspersky Lab’s blog described PowerGhost. “The malware, which we dubbed PowerGhost, is capable of stealthily establishing itself in a system and spreading across large corporate networks, infecting both workstations and servers. The malicious program uses lots of file-less techniques to remain inconspicuous to the user and undetected by antivirus technologies. The victim machine is infected remotely using exploits or remote administration tools. During infection, a one-line PowerShell script is run that downloads the miner’s body and immediately launches it without writing it to the hard drive.”
Being it is a file-less virus, PowerGhost easily bypasses such protective programs. Antimalware applications are not designed to detect malware from just a few lines of code in a PowerShell script, which only appears in a plain text file if examined carefully. Any virtual coins produced are sent to the virus authors; the script is instructed to look for another computer on the same network with similar vulnerabilities, and penetrate it next.
David Emm, a Kaspersky Lab security researcher further explained further. “PowerGhost raises new concerns about crypto mining software. The miner we examined indicates that targeting consumers is not enough for cybercriminals anymore—threat actors are now turning their attention to enterprises, too. Cryptocurrency mining is set to become a huge threat to the business community.”
His conclusion is supported by the opinion of Kaspersky Malware Analyst, Vladas Bulavas who says, “The miner we examined indicates that targeting users is not enough—cybercriminals are now turning their attention to enterprises too,” said Bulavas. “And this makes cryptocurrency mining a threat to the business community.”
PowerShell is a highly praised command line interpreter, as it extends the functionality of scripting beyond the capability of batch files. It is a rich scripting command line service that enables advanced functionality usually seen only with GUI-based tools. Kaspersky also discovered more about the viruses functionality, as one version has a different payload than just cryptocurrency-mining malware.
Kaspersky’s Blog further stated, “In one PowerGhost version, we detected a tool for conducting DDoS attacks. The malware writers obviously decided to make some extra money by offering DDoS services.”
System administrators would be smart to carefully review whether or not a computer needs the PowerShell service. Proactively turning it off if it is, in fact, pointless will close the attack surface and limit the possibility of PowerShell scripting malware, like PowerGhost, from running.