Two Nasty No-Ransom “PewDiePie” Ransomwares, Trouble For Many
Obsession really goes a long way for people to get out of their way to cause trouble for others. As PewDiePie emerges as a Youtube sensation, his fanbase grew to an unprecedented level for a YouTube personality. Unfortunately, some of his fans went overboard, their inner script kiddie by modifying ShellLocker ransomware, creating new ransomware now known as PewDiePie Ransomware.
The ransomware distincts itself from other ransomware families, as it is 100% destructive malware. It was poorly developed by a script kiddie, hence it lacks the command and control server that holds the decryption key. That means anyone who will fall for PewDiePie ransomware has straight forward way to decrypt the encrypted files, even if the victim wants to pay the ransom, the malware simply has no facility to accept the payment, the functionality is not there.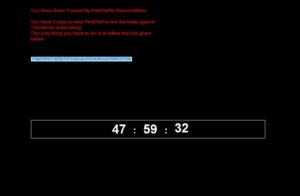
Inspecting the malware reveals that it just encrypts user files, without any option in the code that instructs it to save the decryption key either inside its own cache or to an external server. Another version of PewDiePie-inspired ransomware is named PewCrypt, it was developed using the Java language, hence it can easily target all computers that have an installed Java virtual machine.
PewCrypt Ransomware is different from the earlier malware, given that it has the complete facility to decrypt the user’s data, but there is a huge catch. It does not ask for any ransom, its unknown authors do not desire any financial gain out of it, but rather seem like consider his creation a joke connected with PewDiePie’s Youtube channel subscription numbers. The locked user files will only be decrypted once PewDiePie Youtube channel reaches 100 million subscribers. At the time of this writing, the channel only has 90,544,685 subscribers, it will surely take a while to reach the 100 million thresholds, given that the channel basically already saturated its audience.
At the end, the author of PewCrypt under the alias 000JustMe realized the possibility of authorities taking him under custody and he will be treated as a cybercriminal. He released the sourcecode of PewCrypt on GitHub, stating in the README.md file that “The author does not assume ANY responisblity for the use or abuse of the source or parts of it” (yes, including the typo). He also included a decryption tool in his GitHub page, but it is rather crude given it is a command line tool. The author seemed abandoned any further developments of the ransomware, PewCrypt is just a rogue ransomware in the Internet looking for the next vulnerable victim to infect, without asking for any ransom payment.
Emsisoft, an antimalware vendor steps-in just in time with their free decrypter, which is available for download at https://decrypter.emsisoft.com/pewcrypt. “PewCrypt is a ransomware written in Java that uses AES and RSA to encrypt a victim’s files, adding the extension “.PewCrypt”. The malware then asks the victim to subscribe to PewDiePie. The author supposedly released this as a “joke” in 2019 – but be assured, ransomware is no joke, ever. To use the decrypter, you will require the “AES.key” file left on the desktop by the malware,” explained by Emsisoft.
Also, Read :
Printers Hacked Again by PewDiePie Supporters
Fileless Ransomware: The Next Big Threat For The US In The Waiting