HTTPS Phishing Websites on the Rise. Here’s what you Need to Know.

A recent spike has been seen in HTTPS phishing websites that use Domain Validated SSL certificates to help hackers pilfer users’ personal data. A Discussion of the trend and potential solutions follows…
Phishing is on the rise. With the internet becoming a bigger part of our lives every day, this was bound to happen.
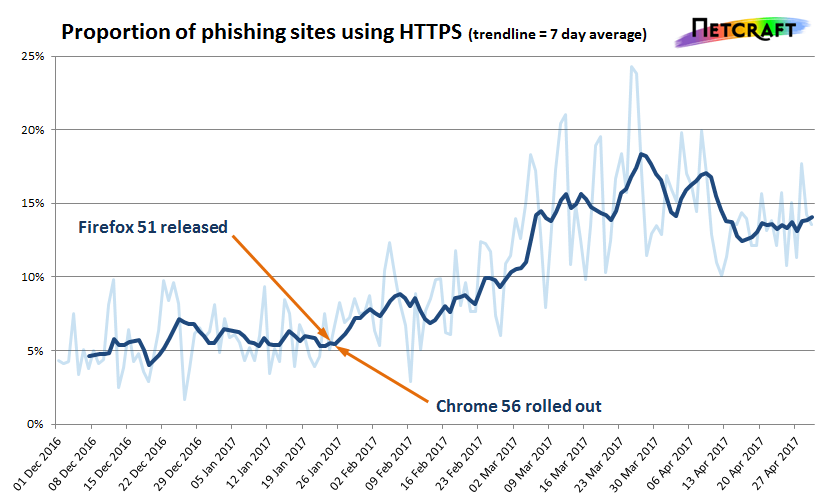
Experts say there are other reasons for the uptick. New trends in the SSL ecosystem contribute to the rise in phishing. With the release of Chrome 56 and Firefox 51, Google and Mozilla intent to change their connection security UI (User Interface) from the somewhat unnoticeable padlock icon to a more obvious and appealing green “Secure/Not Secure” binary. Despite this change, with the rapid proliferation of free SSL certificates, phishing websites are beginning to get SSL certified, meaning they’d be marked “secure.” Hackers can use this to lure users, believing they are safe, into sharing data with them.
The Current Scenario
In analytical post on the Netcraft website says, “…there has been a dramatic increase in the number of phishing sites making use of HTTPS. If the new browser behaviour has driven this change—and the timing suggests it might have—then it may have also had the unintended side effect of increasing the efficacy of some phishing sites. Phishing sites that now use HTTPS and valid third-party certificates can appear more legitimate, and therefore increase the likelihood of snaring a victim.”
Netcraft used this image to show the rise in HTTPS phishing websites since the changes in browser UI came into effect:
SSL authorities have increasingly been issuing certificates to many phishing sites. Security expert Vincent Lynch, the encryption expert at The SSL Store™ wrote a piece on this in March, called Let’s Encrypt had issued over 14,000 SSL Certificates issued to PayPal phishing sites. There are many instances of fake versions of prominent websites. Fake phishing logs on Apple ID pages, AOL phishing pages, fake Yahoo sign-in pages, and Microsoft phishing pages have all been seen. All are marked as secure.
Tech-savvy internet browsers may recognize such websites as fake phishing websites. But the average internet user won’t. Most people can easily be lead to share personal data over a dangerous phishing website that is nonetheless marked “Secure.”
Is there a solution?
As things are, with the new UI in place, HTTPS phishing websites are becoming common. What is to be done? Patrick Nohe, the Editor-in-Chief of Hashed Out, answers this in a blog post. Says Nohe, “The current browser UI is making the internet less safe. It lends credence to HTTPS phishing websites—regardless of its original intentions… To fix this, the browsers need to get rid of the indicators for Domain Validated SSL certificates. DV SSL does not have end user authentication. Anyone can get it—including phishing websites. This move should coincide with the browsers’ final deprecation of HTTP—when all HTTP sites begin to be marked ‘Not Secure.’ Google aims to accomplish this within the next year.”
Indeed, phishing websites are using anonymous Domain Validated SSL certificates to avoid being identified. Patrick Nohe has this to say about this troubling phenomenon: “Regardless of to what degree, the current UI helps HTTPS phishing. That cannot continue. The DV visual indicator must go.”
Related Blog
PayPal Phishing Scam Coming From Official PayPal Email Address