The Common Factors in Phishing
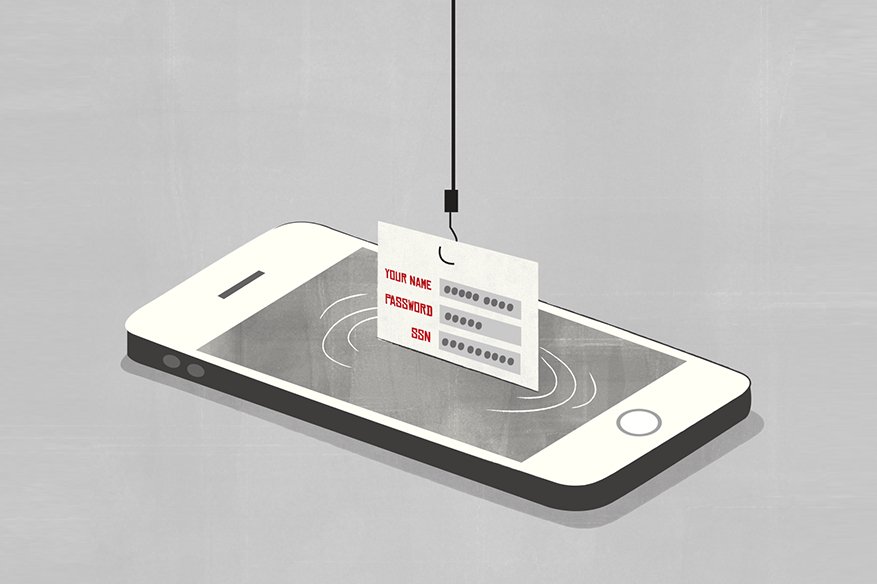
Nowadays, the Internet plays a significant role in online commerce and business activities. However, the weak security awareness of users on the Internet and, a strong motivation for profit attracts cybercriminals to earn quick money in this field. Security risks on the Internet have grown exponentially since the online services have become more popular. This risk can be harmful and undesirable events may occur in different applications, which possibly have some security gaps. There may be a risk that personal and sensitive data can be hijacked over the unprotected Internet lines.
A common factor among the majority of phishing sites is that they mislead users to believe that they are legitimate sites. Thus, recognizing phishing sites is basically an authentication problem between users and servers. Applications on the Web normally involve user authentication before getting access to a requested source. Authentication for users differs from simple to strong. It depends on security policies that are sat upon resources or services. For example, a clear text password-based authentication will suffice to enter a Web forum whereas an online banking requires the use of certificates and a policy of key infrastructures.
Some phishing attacks are technically more sophisticated and make use of well-known vulnerabilities in a popular web browser,s enabling installation of malicious software that collects sensitive information about the user. Rock Phishing Kit, Keyloggers, Session Hijacks, Content Injection phishing, “universal” man-in-the-middle phishing kit and search engine phishing are some types of phishing attacks. Some of the solutions are Phishing blacklist, email authentication, two-way authentication, one-time passwords, etc.
Companies are constantly trying to strengthen their online security. There is no absolute way to overcome spam and phishing. Institutions and users generally must rely on a distributed, multi-tiered defense as phishers have turned to a distributed, multi-tiered system of attacks.
Below are some tips to lessen the chance of falling for phishing spam:
Educate the users
Nothing can defeat a cybersecurity system if the users are educated. Awareness of phishing and the narrative of phishers need to be planted in the minds of the users. Social Engineering is a ballgame where very trusting individuals end up in trouble.
Establish a phishing reporting system
IT teams need to establish protocols on how end-users report phishing to them. This needs to be effectively laid-out as a wrong move can cause major damage. One of which is accidental clicking of website links in the phishing email. An accidental link is enough for the attackers to take over the system.
Use two-factor authentication tokens
This prevents successful take-over of user accounts since the two-factor authentication system provides a secondary password.
Review installed web browser regularly
Several companies today, offer plug-ins for the browsers. These plugins can help to some extent keep our sensitive data secure. They save confidential information and when this information is used again they check if the corresponding website is the one which was visited previously. If not, they prompt the user informing that it can be a phishing website, offering to block it.