NFC Vulnerability May Promote Ghost Screen Taps

Convenience vs Security, that is the frequently recurring theme when it comes to cybersecurity nowadays. Every time a new technology opens its doors to more convenience is when it becomes the new kid on the block when it comes to vulnerabilities. Here in hackercombat.com, we are eager to tell you over-and-over again our dear readers that convenience is the natural enemy of security. The newest issue of this convenience vs security theme has something to do with NFC, and the new attack proof-of-concept presented by Waseda University researchers in Tokyo which they aptly named Tap ‘n Ghost.
The 18-page paper released by a team of three researchers named Tatsuya Mori, Seita Maruyama and Satohiro Wakabayashi demonstrated the vulnerability of NFC feature built-in with many mainstream smartphones sold today. They described it as a combination of a Ghost Touch Generator and TAP (Tag-based Adaptive Ploy), that gives attackers at close range the capability to generate “Ghost Taps” against a target device, through a special combination of a battery pack, high-voltage transformer, an off-the-shelf 5mm copper sheet, NFC writer and a single-board computer like the Raspberry Pie/small laptop.
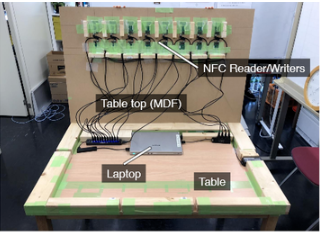
The above image is the proof-of-concept contraption that can be installed in any seemingly ordinary table in a restaurant, coffee shop or any public store. NFC communicates wirelessly in the range of just between 4 to 10 centimeters, with a rigged device such as the above the malicious attacker can then connect to the victim’s NFC-enabled smartphone (of any device with an NFC feature). It can then tell the target smartphone to open a specific website automatically. The attacker can also pretend to issue an innocent request for Bluetooth pairing or Wifi connection attempt, which fortunately requires user-permission to proceed.
Versions of Android from 9.0 or older has the convenient behavior of trusting all NFC pairing attempts when it detects one is something near. The contraption comes with copper interconnects which can produce enough electrical disturbance within the NFC range, enabling the phone to perform Ghost taps, no different from a user tapping his phone to perform an action. At first glance, this sounded like science fiction at first, but the trio of researchers showed to the presentation how these rogue taps can be generated to “provide permission” to the ghost Bluetooth pairing or wifi connection attempts mentioned earlier, completing the whole process.
At the time of this writing, the following mainstream Android devices from Sony, Sharp, HTC, Asus, Fujitsu, and Samsung were known to be vulnerable:
- Xperia Z4
- Galaxy S6 Edge
- Galaxy S4
- Aquos Zeta SH-04F
- Nexus 9
- Arrows NX F005-F
- Nexus 7
It is now yet known if current devices sold in the market with NFC are also affected, but the three researchers mentioned that the false touch vulnerability may also exist on newer devices as the protocols of NFC remains the same across generations of devices. The IEEE Symposium on Security and Privacy shared a video detailing the exact components of the Ghost ‘n Tap device, its operations and basic understanding of the snooping process against NFC devices.
This vulnerability may one-day prompt smartphone vendors to ship their mobile phones with NFC disabled by default. This new disabled by-default behavior will also benefit Android users, as the device do not need to consume more energy to power-up the NFC component of the smartphone even if the user does not currently need it.
Also, Read:
Why You Need to be Careful About the BlueKeep Vulnerability
Belkin Wemo Insight Smart Plug Vulnerability Remains Exploitable
Google Photos Vulnerability that Lets Retrieve Image Metadata
New Google Chrome Zero-Day Vulnerability Detected
Important Features of Vulnerability Scanners