New Hybrid Computing, Same Security Concerns

Pulse Secure, with the cooperation of IDG Connect has released its 2019 State of Enterprise Secure Access research paper, detailing how cloud computing has influenced companies’ daily operations and how secure the vendor platforms are. The business world is moving to the new platform, the cloud, slowly migrating from the decade-old “internally-located” servers for their applications and day-to-day activities. That ultimately means the Internet, which was considered as an “external network” is now actually the direct computing platform for storing files and host desktop applications.
In the report, Pulse Secure has highlighted the importance for companies, large and small to implement “ZeroTrust” across the board. It is a policy model where everything needs to be verified before permissions can be delegated. This is with strong compliance with the goal of any company to have effective identity management, device management, and secure protocols. The report also recognizes that mobile computing workforce is here to stay, but through various technologies including VPN (Virtual Private Network) are highly utilized to provide some level of privacy and security for the corporate mobile users.
The study conducted by the IDG Connect and Pulse Secure partnership covers 300 carefully selected Senior IT Leaders from Germany, Switzerland, United States Austria and UK in order to measure their IT security challenges in their company’s respective daily operations, deployment of software/hardware strategies, degree of confidence of the organization that risks can be mitigated on time and the methodology used in order to arrive at a decision on what products and services to sign-up for to “fortify corporate security”.
Years ago, many organizations are highly dependent on their company’s local data center for their storage, while applications were still often used and loaded from the local PC hard disks. More and more organizations depend on public and private cloud services in order to simplify deployment of critical applications to the organizations.
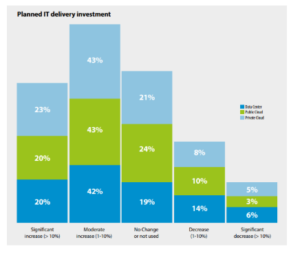
Secure Pulse accounted that a whopping 63% of IT professionals and leaders surveyed shows the tremendous growth of dependence with Public and Private cloud infrastructure which started last year and continuing this year, 2019. Organizations are moving away to purely desktop-based applications and local hosting of files but started strong adoption of cloud-storage and cloud-based apps similar to what used to do with a desktop version of the software.
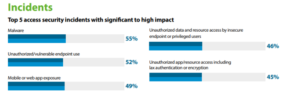
The report also featured how the 300 IT security leaders view the problems surrounding corporate IT. The top IT security and privacy concerns raised by them are:
- Malware
- Unauthorized/vulnerable endpoint use
- Mobile or web app exposure
- Unauthorized data and rouse access by insecure endpoint or privileged users
- Unauthorized app/resource access including lax authentication or encryption
High Impact gaps are also presented by Secure Pulse which make organizations becoming desperate with a quick solution, something that can never be achieved in the real world:
- Poor user, device discovery and mobile computing exposure
- Application availability
- Uncoordinated authorization
- Inconsistent, incomplete enforcement, week device access and configuration compliance
- Security gateway sprawl, inconsistent/incomplete remediation
“Our survey suggests that the majority of respondents are experiencing issues in application availability (81%) in terms of ensuring responsiveness and reliable access for users. This may suggest a need to improve application usage analytics and load balancing automation,” the report summarized.
Also Read: