First 5 Things To Do After Activating A New Android Device
Our mobile devices contain a lot of personal information, even more than on our computers. We go all day with our mobile phone, we can not leave home without it, and if we lose it or it is stolen it becomes a drama, which can be even greater if we do not have our device protected. The Android operating system has been adding over the years’ security features that allow us to have very well protected our Android and our data so that only we can access and avoid dislikes if our device falls into the wrong hands or if we install any application malicious.
Here are some tips in order to help lock down an Android device:
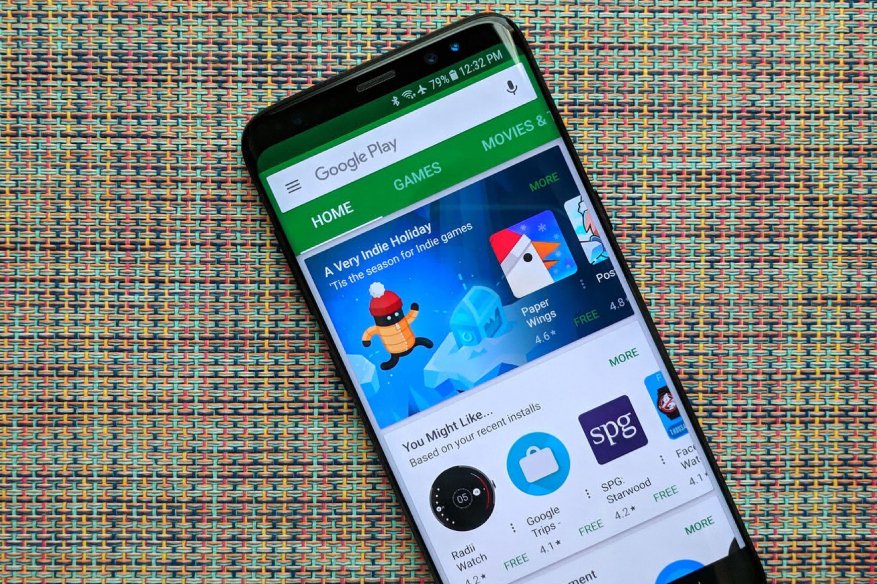
1. Google Play Protect
By default, Google installs a real-time updating antimalware system in Android. It is part of the Google Play Services system, which all Android handset manufacturers install by default, except for Amazon devices and those Google-free devices made in China, for the Chinese citizens. Google Play Protect automatically scans all apps before it gets installed and the good thing about it is its maintenance-free nature. Users don’t need to manually update it with new signatures to detect new malware; it updates itself in the background while Google Play Store is open.
2. Use a lock screen
If we want to protect our Android, it is mandatory to put a screen lock. This can be a pattern, a PIN, a password or our fingerprint if the device has a reader. Of course, if we choose a pattern let’s put one that is not easy to predict. It is configured in Settings> Security> Screen lock. If it bothers us having to be unlocking the device every time we turn on the screen we can use the Smart Lock that released Android Lollipop. This automatic unlocking will avoid having to put the pattern or PIN when it recognizes our face, we have it in hand, we are at home, etc. It is configured in Settings> Security> Smart Lock.
3. Only use the Google Play Store for downloading apps
The safest way to install applications and games is to do it from Google Play. The shop already analyzes and approves the applications, with which malicious applications are rarely leaked. It is advisable to deactivate the option Settings> Unknown origins. To have the peace of mind that all the applications that we have installed are safe, nothing better than to activate the application verifier. In the Google Settings> Security, we have to activate the option “Search for security threats on the device” and “Improve the detection of harmful applications.”
4. Take control of permissions
From Android Marshmallow we can manage the permissions of the applications, a security measure that will give us more control and privacy. In Settings> Applications> Advanced options> Application permissions we can decide to what type of information and functions each of the applications can access.
5. Encrypt the device
Available since Android 4.0 Ice Cream Sandwich is full device encryption support. The encryption process is very slow, lasts more than an hour, and then every time we turn on the phone, all the data has to be deciphered, which slightly affects the performance.
Related Resources