DOS Attacks and Free DOS Attacking Tools

Denial-of-service (DoS) attacks are the antecedent to DDoS attacks. Earlier, DoS attacks were the main source of disrupting computer systems on a network. It originates from a single machine and may look very simple; a basic ping flood attack can be accomplished
By sending ICMP (ping) requests to a targeted server, it processes and responds, and this way you can accomplish a basic ping flood attack. By using built-in terminal commands anyone with a networked machine can launch this type of attack. The intricate DoS attacks involve using packet fragmentation.
In simple terms –
- DOS (Denial of Service) is an attack performed on a computer or network that prevents accessibility of system resources to users.
- The attacker overloads his resources and floods the victim system with malicious traffic.
- Online DOS attacks can do temporary or permanent damage to a website. It can also slow down network performance.
A number of different attack tools are available for free on the Internet. Some of these tools have legitimate purposes, as security researchers and network engineers perform stress tests against their own networks. Some attack tools are specialized and only focus on a particular area of the protocol stack, while others will be designed to allow for multiple attack vectors.
Types of DOS Attack
There are basically three types:
- Application-layer DDOS attack
- Protocol DOS attack
- Volume-based DDOS attack
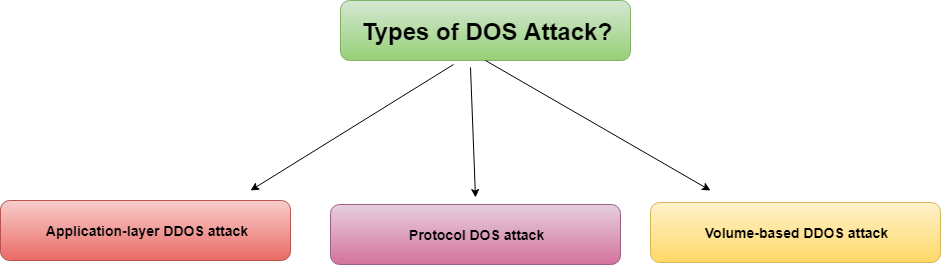
Application layer DDOS attack: Application-layer DDOS attacks are attacks that target Windows, Apache, OpenBSD, or other software vulnerabilities to perform the attack and crash the server.
Protocol DDOS attack: A protocol DDOS attack tools is a DOS attack on the protocol. This category includes Synflood, Ping of Death, and more.
Volume-based DDOS attack: This type of attack includes ICMP floods, UDP floods, and other kinds of floods performed via spoofed packets.
Online Free DDoS Attack Tools: There are many tools available for free that can be used to flood a server and perform an attack. A few tools also support a zombie network to perform DDOS attacks. For this post, we have compiled a few freely available DOS attacking tools.
Most Popular DDoS Attack Tools in 2024
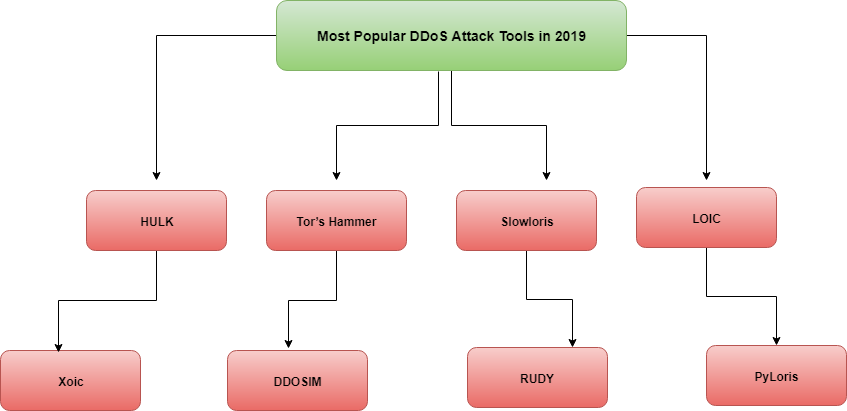
1) HULK
HULK – stands for HTTP Unbearable Load King. It is a DoS attack tool for the web server and is created for research purposes.
- It can bypass the cache engine.
- It can generate unique and obscure traffic.
- It generates a great volume of traffic on the web server.
2) Tor’s Hammer
The free DDoS attack tools are for slow post attack and are created for testing purposes.
- With this tool, the attack can be made on Apache and IIS servers.
- If you run it through the Tor network then you will remain unidentified.
- In order to run it through Tor, use 127.0.0.1:9050.
3) Slowloris
Slowloris is used to down the server and make an online DDoS attack.
- It bombards authorized HTTP traffic to the server.
- It doesn’t affect other services and ports on the target network.
- This attack tries to keep the maximum connection engaged with those that are open.
- It achieves this by sending a partial request.
- It tries to hold the connections as long as possible.
- As the server keeps the false connection open, this will overflow the connection pool and will deny the request to the true connections.
4) LOIC
It is a free and popular DDoS attack tool. LOIC means Low Orbit Ion Cannon and is used for the online DDoS attack.
- It is easy to use, it sends UDP, TCP, and HTTP requests to the server.
- It can do the attack based on the URL or IP address of the server.
- Within seconds, the website will be down and it will stop responding to the actual requests.
- It will NOT HIDE your IP address. Even using the proxy server will not work. Because in that case, it will make the proxy server a target.
5) Xoic
It is a simple DoS attacking tool attack can perform a DOS attack on any server with an IP address, a user-selected port, and a user-selected protocol. It comes with an easy-to-use GUI, so a beginner can easily use this online DoS tool to perform attacks on other websites or servers.
- It is easy to use.
- It provides three modes of attack.
- Testing mode.
- Normal DoS attack mode.
- DoS attack with TCP or HTTP or UDP or ICMP message.
6) DDOSIM
DDOSIM, known as DDoS Simulator. This tool is for simulating the real DDoS attack and can attack on the website as well as on the network.
- It attacks the server by reproducing many Zombie hosts.
- It can make an attack on the application layer.
- These hosts create a complete TCP connection with the server.
- It can do HTTP DDoS attacks using valid requests, as well using invalid requests.
7) RUDY
RUDY stands for R-U-Dead-Yet, and uses a long form field submission through the POST method.
- Interactive console menu.
- You can select the forms from the URL, for the POST-based DDoS attack.
- It identifies the form fields for data submission. Then injects the long content length data to this form, at a very slow rate.
8) PyLoris
This is basically developed for testing to make a DoS attack on the server, this tool uses SOCKS proxies and SSL connections.
- The attack can be made on HTTP, FTP, SMTP, IMAP, and Telnet.
- It has an easy-to-use GUI.
- It directly makes an attack on the service.
Conclusion – Online Free DDoS Attack Tools
The list of tools mentioned in this article are the most popular ones for making a DDoS attack. These tools can be great resources for performance and security testing.
Related Resources:
How to Protect Businesses Against DDoS Attacks