Today's Featured

Ways to Mitigate Risk in Cybersecurity: Cybersecurity Risk Management
Cyber threats can wreak havoc on businesses, from data breaches to loss of reputation. Luckily, there are effective strategies available that can reduce cybersecurity risk. Avoidance is one of the…
Read More
Zero Trust Architecture
Zero trust security takes an “never trust, always verify” approach to access control. Access is only granted once an individual’s identity and context have been confirmed through multifactor authentication and…
Read More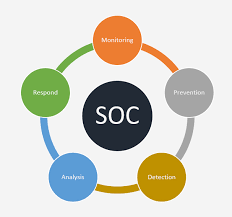
What Is a Security Operations Center (SOC)?
A Security Operations Center (SOC) specializes in monitoring and analyzing data to detect cyber threats and prevent attacks from them. They work to sort actual threats from false positives before…
Read More

XDR vs SIEM Security Information and Event Management
The Extended Detection and Response Platform (XDR) ingestion and correlation technology captures and correlates high-fidelity data across your security layers, such as endpoint, network, logs, cloud services and identities to…
Read More
Best Free EDR for Windows PC
Endpoint detection and response (EDR) tools offer businesses that employ hybrid work models or remote employees an extra layer of cybersecurity protection. Utilizing artificial intelligence (AI) and machine learning (ML),…
Read More
Free EDR Solutions for Home Users in 2025
EDR can detect and respond to emerging and advanced cyber threats quickly and efficiently, making it an essential component of modern business ecosystems. Beyond signature-based detection capabilities, its features go…
Read More
Cloud Security Essentials
Cloud security involves employing perimeter defenses like firewalls, IDPSs and VPNs as well as guaranteeing isolation through network segmentation and virtual LANs while monitoring traffic for anomalies and threats –…
Read More
Antivirus Software
Antivirus software protects devices against viruses, malware, and other cyberthreats by detecting, quarantining, and deleting malicious code. Modern antivirus products also offer additional security features such as password protection, identity…
Read More
How to Protect Against Ransomware Attacks?
Criminal hackers employ ransomware attacks against their targets by encrypting their data and demanding that a ransom be paid within an allotted timeframe or risk losing it forever. When an…
Read More
Protecting Your Website From DDoS Attack
Distributed denial-of-service attacks pose an increasing threat to organizations, with even some of the largest firms suffering significant disruptions from such attacks. Attackers use botnets of compromised IoT devices to…
Read More






