The Story of Security in the History of Computing
During the decades gone by, a company that used a computer system for some sort only had two variables to cover when it comes to computer security:
- External floppy disk
- Prank viruses
Life was easier since floppy disks had right protect notch which, when set prevents the contents of the disk from being modified. This was used to help prevent the spread of malware, as infection happens when an infected machine as write access to a foreign disk, and that same disk is reused with a non-infected computer. MS-DOS and an early version of Windows like 95 and 98 were light operating systems; they can be installed in less than two hours hence reformat and reinstall is not much of a big deal.
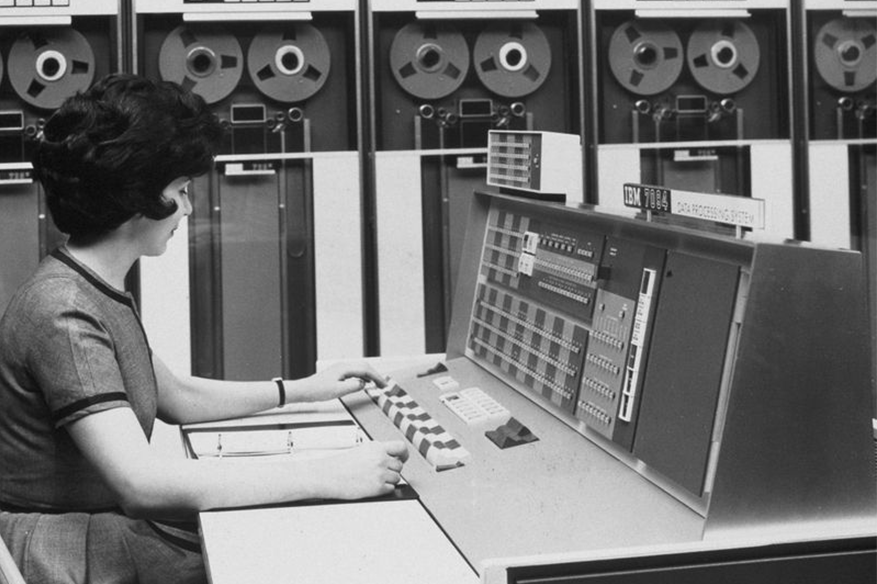
The early malware was also programmed to create the feeling of fame for the virus authors, more of a prank than a money-making scheme which they evolved to today. Companies experienced their first taste of networking technology long ago even before MS-DOS of the 1980’s was developed, however, it took till the introduction of Windows NT in 1993 that enabled seamless networking. As the world was facing a crowded networking market, when there was more than a dozen networking protocol, we basically end-up just standardizing into one common protocol today TCP/IP.
TCP/IP is the protocol of the Internet age, enables all types of network-aware devices to communicate with one another. This made it easy for malware authors to standardize their strategy as well, they redefined their goals of not destroying the user’s OS at the very second of infection, but to take advantage of it. There is money to be earned from virus development, and cybercriminals innovate at the same phase as the development of any other mainstream software in the market.
The growth of the malware black market industry is proportional to the growth of the antimalware industry. At the time of this writing, there were 45 antimalware vendors, Microsoft had recognized as compatible with Windows 10. It can be seen as both beneficial and non-beneficial to any corporations that want to earn a profit and any individual users that want to use a computer for whatever goal they want. The “Information Superhighway”, the common moniker of the Internet in the late 90’s, was the very channel where the virus infection spread.
This made the Internet both the source of the malware infection and source to cure for malware infection. Floppy disk and USB flash drive-based infections were no longer relevant, as people started to scan them before use a long time ago. Modern antimalware also automatically scan external media prior to giving the OS the go-signal to use the files it contains. The software has become more functional yet more complex, the size of today’s programs was not even imagined by developers 20 years ago. The size establishes more complexity, the more complex the software is the wider the attack surface.
Users of corporate computers need to be aware of strict IT policies imposed, given that there is no single cog in the whole machine that covers system security. It will always be a sophisticated series of algorithms and codes which makes up the software side of the computer, prone to bugs and vulnerabilities. Organizations huge or small are all facing the new normal, software should be updated as soon as it reaches the hard drives. Updates should never be delayed beyond a reasonable time frame, as the longer the delay, the wider the attack surface.
User education is the key to system security, to user privacy and computing safety. There is no shortcut to it; no single cybersecurity vendor can be the be-all and end-all, they are just offering 1, 2, 3 or 10 cogs in a huge machinery we know as a computing device today.