Users of the open-source Apache Struts 2 web app development framework have been urged to update their software following today’s disclosure of a critical remote code execution vulnerability that leaves…
Read MoreSearch Result for "open-source"

The source code of Snapchat, the very popular social media app, was posted online on the Microsoft-owned repository GitHub. A GitHub repository called Source-Snapchat and with a description “Source Code…
Read More
Aside from the development of the Linux kernel, where numerous known names in the Internet industry are in constant partnership, it really is rare for companies to partner with each…
Read More
The crypto-jacking malware, a new cyber threat that has been found on systems and servers within business networks, websites and many IoT (Internet of Things) devices, helps criminals use business…
Read More
The U.S. Government officials have accused Russian cyber actors of attacking key U.S. Infrastructure across a wide range of industries- aviation, nuclear, the electric grid etc. The allegations are made…
Read More
Cyber security researchers have reportedly discovered what they think is the first Krotin-based malware affecting the Android OS. The discovery has been made by researchers at Trend Micro; a Trend…
Read More
Cryptocurrency mining malware is spreading at a fast rate, and this time the criminals are making use of Facebook Messenger to infect people as the message looks genuine from friend’s….
Read More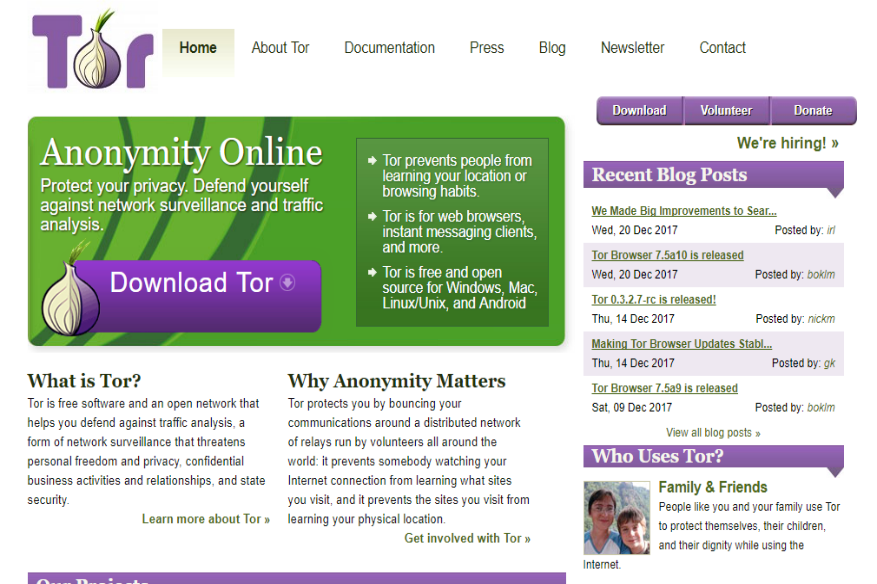
What is Tor? Tor is a free, open-source browser that functions using the onion routing process. Tor works on all kinds of internet protocols- HTTP, HTTPS, FTP, Gopher etc. The…
Read More
Android devices are a standout amongst the most vulnerable operating system due to its open-source nature. Nevertheless, what choice the user has if he is given a phone that is…
Read More

